
If your application sends or receives data on the network, it is important to protect the privacy and integrity of personal information and to protect against data breaches and attacks. You must use the Transport Layer Security protocol (TLS) protocol to protect the content being transported and to verify the server receiving the data.
When you connect via TLS, the server issues a certificate or certification chain. You can restrict the collection of server certificates that your application trusts by posting their public key identities on your app. Here’s how to get started.
When to use a pinch
By default, when your application is connected to a secure TLS network, the system will evaluate server integrity by default. Most apps can meet their security requirements by relying on this feature: However, some applications may need to restrict the collection of trusted certificates further.
For example, your application may meet regulatory requirements that determine which specialized certification authorities (CAs) can be trusted. While Apple Platforms ensures that only trusted CAs are involved by default, your application may use an identity plug-in to further limit CA sets to those associated with a specific government or organization.
Plugging can’t solve your app’s trust requirements – just tighten them. You must still meet the system’s default credentials when using public key certificates involved in the TLS network connection.
Note: When you configure your application to protect certain public keys for a server, it will not be able to connect to that server unless those public keys are involved. As a result, if your server deploys new certificates that change public keys, your application will not be able to communicate. At that point you need to update your app with a plug-in configuration that reflects the new set of public keys.
Think long and hard
If you want to use identity plug-ins in your app, consider creating a long-term strategy that captures both planned and unplanned events to prevent plug-in failures.
Your application can provide a better experience by connecting CAs public keys instead of servers. In this way, you can deploy server certificates with the same public key signed by the same CA without having to attach configuration upgrades.
You can also consider plugging in more than one public key, especially when mounting server identities. This way, your application can still connect to the configured servers, even if the servers delete certificates.
Also, if you are unable to connect to the server during a plug-in problem, plan to provide a restore experience in your app. First, consider the ways in which your app experience could be affected and come up with solutions to any negative side effects. Can the app still work without that connection, and can you give someone a temporary recovery?
You also want to plan a last resort. One way to fix plug-in failures is a new plug-in configuration provided by App Update. Consider that option depending on how you use your app.
For this purpose, we strongly recommend that you try different applications and error points when testing your app by obtaining additional public key certificates and modifying your server configuration.
How to plug CA public keys
A plugged CA public key must appear in the intermediate or lower certificate in the certificate chain. Plugged keys are always associated with a domain name, and the app will not be allowed to connect to that domain unless the plug-in requirement is met.
For example, to ask if there is a specific CA public key when you contact example.org Domain name, the following entries to Info.plist Your application file.
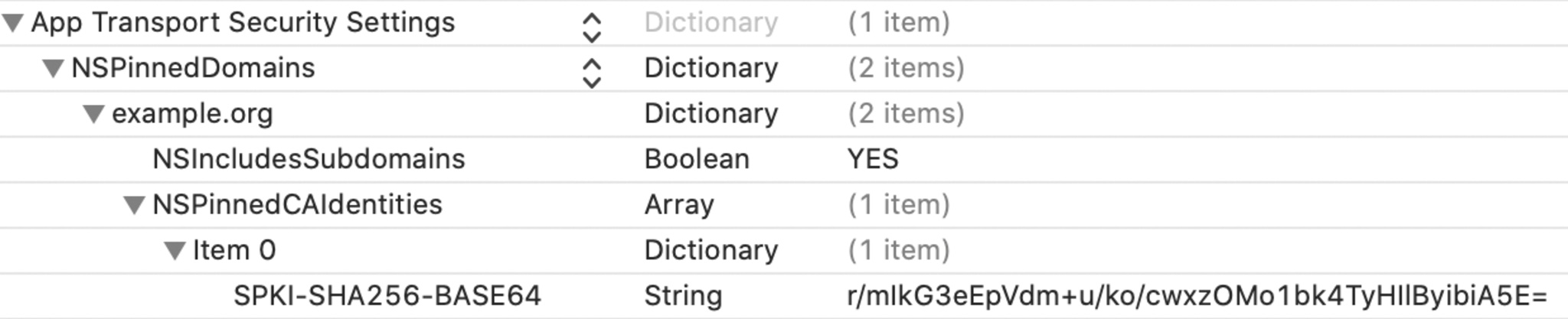
<key>NSAppTransportSecurity</key>
<dict>
<key>NSPinnedDomains</key>
<dict>
<key>example.org</key>
<dict>
<key>NSIncludesSubdomains</key>
<true/>
<key>NSPinnedCAIdentities</key>
<array>
<dict>
<key>SPKI-SHA256-BASE64</key>
<string>r/mIkG3eEpVdm+u/ko/cwxzOMo1bk4TyHIlByibiA5E=</string>
</dict>
</array>
</dict>
</dict>
</dict>In this example, the pinned public key is associated with. example.org And as subdomains math.example.org And history.example.orgBut it does not relate to this. advanced.math.example.orgOr ancient.history.example.org.
The key to the public key is the X.509 Certificate DER-encoded ASN.1 subject to the public key information structure such as Base64-encoded SHA-256. The following is a PEM-encrypted public key certificate stored in a file. ca.pemYou can calculate the value of SPKI-SHA256-BASE64 with. openssl Order.
-----BEGIN CERTIFICATE-----
MIIDrzCCApegAwIBAgIQCDvgVpBCRrGhdWrJWZHHSjANBgkqhkiG9w0BAQUFADBh
MQswCQYDVQQGEwJVUzEVMBMGA1UEChMMRGlnaUNlcnQgSW5jMRkwFwYDVQQLExB3
d3cuZGlnaWNlcnQuY29tMSAwHgYDVQQDExdEaWdpQ2VydCBHbG9iYWwgUm9vdCBD
QTAeFw0wNjExMTAwMDAwMDBaFw0zMTExMTAwMDAwMDBaMGExCzAJBgNVBAYTAlVT
MRUwEwYDVQQKEwxEaWdpQ2VydCBJbmMxGTAXBgNVBAsTEHd3dy5kaWdpY2VydC5j
b20xIDAeBgNVBAMTF0RpZ2lDZXJ0IEdsb2JhbCBSb290IENBMIIBIjANBgkqhkiG
9w0BAQEFAAOCAQ8AMIIBCgKCAQEA4jvhEXLeqKTTo1eqUKKPC3eQyaKl7hLOllsB
CSDMAZOnTjC3U/dDxGkAV53ijSLdhwZAAIEJzs4bg7/fzTtxRuLWZscFs3YnFo97
nh6Vfe63SKMI2tavegw5BmV/Sl0fvBf4q77uKNd0f3p4mVmFaG5cIzJLv07A6Fpt
43C/dxC//AH2hdmoRBBYMql1GNXRor5H4idq9Joz+EkIYIvUX7Q6hL+hqkpMfT7P
T19sdl6gSzeRntwi5m3OFBqOasv+zbMUZBfHWymeMr/y7vrTC0LUq7dBMtoM1O/4
gdW7jVg/tRvoSSiicNoxBN33shbyTApOB6jtSj1etX+jkMOvJwIDAQABo2MwYTAO
BgNVHQ8BAf8EBAMCAYYwDwYDVR0TAQH/BAUwAwEB/zAdBgNVHQ4EFgQUA95QNVbR
TLtm8KPiGxvDl7I90VUwHwYDVR0jBBgwFoAUA95QNVbRTLtm8KPiGxvDl7I90VUw
DQYJKoZIhvcNAQEFBQADggEBAMucN6pIExIK+t1EnE9SsPTfrgT1eXkIoyQY/Esr
hMAtudXH/vTBH1jLuG2cenTnmCmrEbXjcKChzUyImZOMkXDiqw8cvpOp/2PV5Adg
06O/nVsJ8dWO41P0jmP6P6fbtGbfYmbW0W5BjfIttep3Sp+dWOIrWcBAI+0tKIJF
PnlUkiaY4IBIqDfv8NZ5YBberOgOzW6sRBc4L0na4UU+Krk2U886UAb3LujEV0ls
YSEY1QSteDwsOoBrp+uvFRTp2InBuThs4pFsiv9kuXclVzDAGySj4dzp30d8tbQk
CAUw7C29C79Fv1C5qfPrmAESrciIxpg0X40KPMbp1ZWVbd4=
-----END CERTIFICATE-----
$ cat ca.pem | openssl x509 -inform pem -noout -outform pem -pubkey | openssl pkey -pubin -inform pem -outform der | openssl dgst -sha256 -binary | openssl enc -base64You can attach multiple public keys to a domain name to promote repetition to your port configuration.
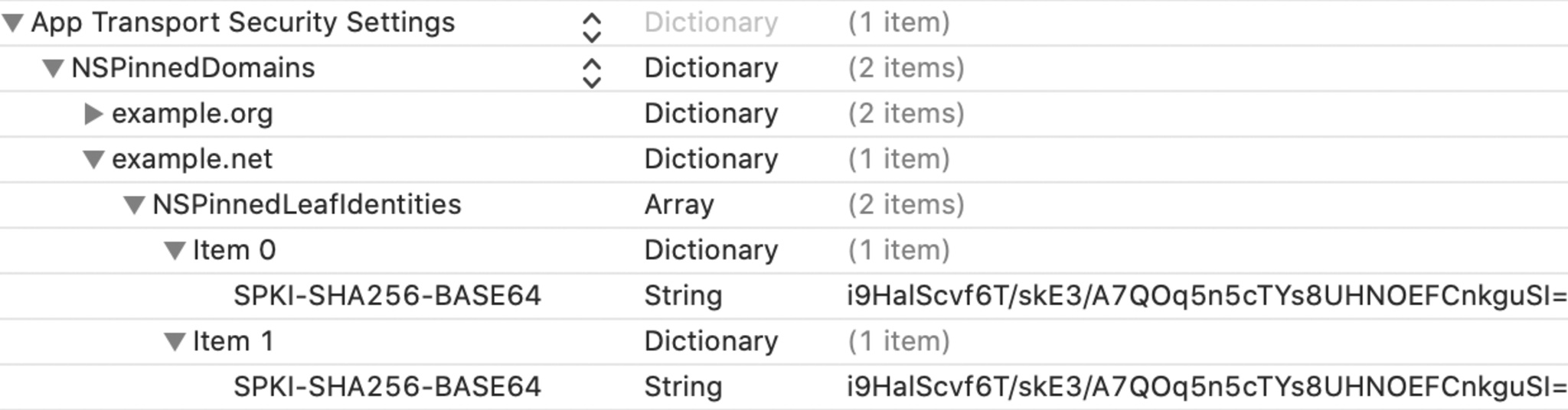
<key>NSAppTransportSecurity</key>
<dict>
<key>NSPinnedDomains</key>
<dict>
<key>example.org</key>
<dict>
<key>NSIncludesSubdomains</key>
<true/>
<key>NSPinnedCAIdentities</key>
<array>
<dict>
<key>SPKI-SHA256-BASE64</key>
<string>r/mIkG3eEpVdm+u/ko/cwxzOMo1bk4TyHIlByibiA5E=</string>
</dict>
</array>
</dict>
<key>example.net</key>
<dict>
<key>NSPinnedLeafIdentities</key>
<array>
<dict>
<key>SPKI-SHA256-BASE64</key>
<string>i9HaIScvf6T/skE3/A7QOq5n5cTYs8UHNOEFCnkguSI=</string>
</dict>
<dict>
<key>SPKI-SHA256-BASE64</key>
<string>i9HaIScvf6T/skE3/A7QOq5n5cTYs8UHNOEFCnkguSI=</string>
</dict>
</array>
</dict>
</dict>
</dict>For example, multiple public keys b example.net Server certificates include individual entries as an item in the negotiation Info.plist Your application file. To meet the requirements for a connection plug example.netThe server certificate must include one of these keys.
Resources
NSApp Transportation Safety



