Posted by Sandeep Patil – Principal Software Engineer, and Irene Ang – Product Manager
of Android Virtual Framework (AVF) Available on select recent Android 14 devices. First introduced in Android 13 on Pixel devices, AVF provides new capabilities for platform developers working on a variety of applications.
At AVF, we are extensively supporting virtualization for Android. Virtualization is widely used to isolate workloads and operating systems from each other. It enables efficient balancing of infrastructure, environments, legacy software compatibility, creation of virtual desktops, and more.
With AVF virtual machines become the core building blocks of the Android operating system, similar to the way Android uses Linux processes. Developers have the flexibility to choose the level of isolation for a virtual machine.
- One-way isolation; Android (the host) can monitor and inspect the contents of the VM. These are commonly used for sandboxing and isolation, allowing multiple operating systems to run on a single machine/device, with one operating system host (Android) controlling all others.
- Two-way isolation (separate VM) Android (the host) and the virtual machine (the guest) are completely separate from each other. Developers who process or store sensitive data can benefit from an isolated virtual machine. An isolated virtual machine has a two-way barrier, where neither the host (Android) nor the VM communicate with each other, except through explicitly agreed-upon communication channels. It has 2 main features.
- The workload and data in the VM cannot be accessed (confidential) from the host (Android).
- Even if Android is corrupted up to (and including) the host kernel, the isolated VM is fine.
Advantages of AVF
Single
With an isolated VM, developers now have the option of trustzone for use cases that require isolation from Android.
Mobility
Virtual machines and the applications running in them are more portable than trusted applets. For example, a Linux-based virtual machine with a Linux application installation will run on all devices that support AVF. This means developers can build an application once and deploy it everywhere. VMAs make porting existing Linux-based applications seamless and easy compared to porting to the TruZone operating system.
Performance
AVF is designed to be lightweight, efficient and flexible. Virtual machines can:
- Be as small as a single C program and as large as a complete operating system as the developer needs;
- to be constant or unceasing;
- Growth or decline in memory as a function of overall system health; And
- Heed Android scheduler hints and low memory warnings.
Extension
AVF was designed with developers in mind. Virtual machines can be customized to meet specific use-case needs. Developers can deploy any VM payload as long as it conforms to specific boot and communication protocols defined by AVF.
In addition to bringing virtualization to Android and enabling sandboxing of all virtual desktops, using AVF isolated virtual machines addresses the following common Android use cases (and more).
- Biometrics: By deploying biometric trusted applets in an independent virtual machine, developers have guaranteed isolation, access to more computing power for biometric algorithms, easier upgrades, and more streamlined deployment regardless of Trezone’s operating system.
- DRM: Widevine enables DRM streaming on Android devices. Once deployed in an independent virtual machine, Widevine updates are easy on all Android devices, regardless of the specifics of the various Treszone operating systems.
Use of AVF
AVF provides simple APIs to query the device’s ability to create virtual machines and their supported types, and to set secure communication paths from the applications and services created by these virtual machines.
For example, to verify the availability of AVF APIs and standalone and standard VMs:
VirtualMachineManager manager =
(VirtualMachineManager)context.
getSystemService(VirtualMachineManager.class);
if (manager == null) {
// AVF not supported
} else {
int capabilities = manager.getCapabilities();
if ((capabilities & CAPABILITY_PROTECTED_VM) != 0) {
// protected VM is supported
}
if ((capabilities & CAPABILITY_NON_PROTECTED_VM) != 0) {
// non protected VM is supported
}
}
Please find more documentation on AVF and its APIs here.
Components of AVF
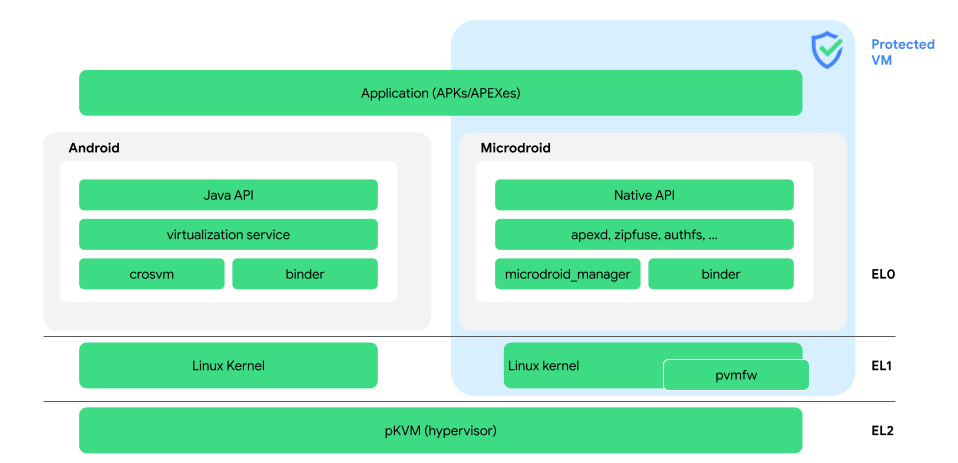
AVF includes framework APIs, a hypervisor, and a virtual machine manager. A hypervisor ensures that virtual machines (including Android) are isolated from each other, similar to how the Linux kernel works for processes. The AVF hypervisor (pKVM), however, has a much smaller (~50x) code base compared to the Linux kernel.
Hypervisor (pKVM)
The hypervisor focuses on open source availability, security, provisioning of tools for VMs, and separation between virtual machines. It has a small attack surface that meets a high level of security assurance. AVF APIs and features are fully supported by the proprietary KVM hypervisor (pKVM).
pKVM is built on the industry standard kernel-based Virtual Machine (KVM) in Linux. This means that all existing operating systems and workloads that rely on KVM-based virtual machines can run seamlessly on pKVM on Android devices.
Virtual Machine Manager (crosvm)
Crosvm, a Rust-based Virtual Machine Manager (VMM) provides the glue between the hypervisor and the AVF framework. It is responsible for creating, managing and destroying virtual machines. In addition, it provides an abstraction layer on top of many hypervisor implementations.
Independent virtual machines
Isolated virtual machines are invisible to Android i.e. any process running in Android cannot inspect, view and tamper with the contents of such virtual machine. This guarantee is provided by the hypervisor.
virtual machines
Virtual machines are similar to isolated VMs except that they are not accessible to Android processes with the correct permissions and privileges.
Microdroid
MicroDroid is an underlying Android OS package created to serve as a template for starting a virtual machine (VM). It provides a familiar environment for developers to build and run their workloads in a VM. MicroDroid uses familiar Android tools and libraries such as Bionic, Binder IPC, and keystore support.
Virtual service
A virtual server manages all guest VMs, isolated or otherwise. It does this mainly by managing crosvm instances. It also exposes the ADL API, which system services or specialized applications can use to start, manage, and stop VMs.
RpcBinder
RpcBinder It is completely new developed for Android Interface Definition Language (ADL). RpcBinder enables communication to virtual machines using the existing Binder wire protocol. This means:
- Developers can write interfaces to virtual machines using a language and infrastructure they are familiar with – AIDL.
- Even if the binding endpoint is moved to a virtual machine, you can simply continue to use the existing ADL interfaces.
What’s new in Android 14?
In addition to making AVF available on more devices, Android 14 introduces a new set of tools to build further with AVF and its components:
- Android System API for AVF
Specialized applications can now use VMs to execute critical workloads that require isolation.
- Hypervisor DevEx Toolkit
Added traceability, improved debugging and monitoring capabilities to provide insights and help platform developers develop in isolated VMs;
- Hypervisor vendor modules
With vendor module extensions, our partners can customize Google Hypervisor (pKVM) to meet their unique needs and differentiate themselves.
- System health improvements
Android 14 Microdroid based VM boot 2 times faster compared to Android 13.